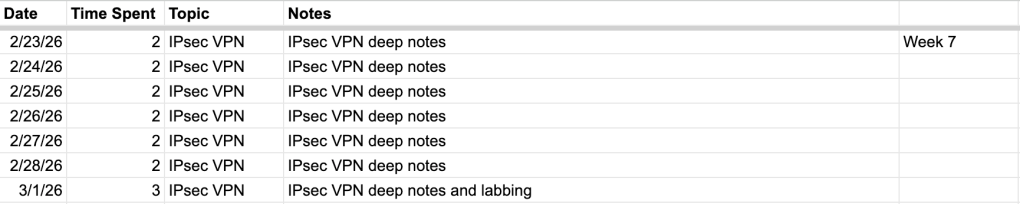
As usual, we start with the tracker for the past week:
I wish I had the time and care to insert that “It’s all X? It always was.” meme with the two astronauts. In my case it would be all IPsec this week. IPsec is near and dear to my heart in that, like BGP, I deal with it just about every single work day. Between standing up new tunnels with partner enterprises or simply thinking about how data traverses our network, IPsec VPNs are involved. The piece here that I’m exciting about as studying is chugging along is getting to lab out IPsec Dial-Up remote access VPNs. Our organization is still on SSL VPN and we’re right up to that time where a migration to IPsec VPN is making its way up the priority list.
One quick lab update. I’ve stood up a “DC” in Azure. A little F1 Windows Datacenter 2025 VM that I’m using to begin labbing out RADIUS, SAML, and LDAP authentication for IPsec dial-up VPN. Luckily I was able to configure it pretty cheap and I’m only sitting at just over $20 a month for the box. Given that I’ll only turn it on when actively using it I’m expecting a dollar or two a month overall. Again, I want to keep providing lab cost updates here just to track the cost comparison of a fully virtual lab in Azure versus investment in a metal server and Hyper-V.
Motivation is better this week. The switch from reviewing routing to beginning a “new” subject is definitely the cause. It’s nice to learn about entirely new subtopics and begin labbing out scenarios I haven’t seen before. Soon enough I’ll be able make use of that FortiAuthenticator eval license I was provided and integrate FAC with IPsec VPN (but I’m going to come back to this during the authentication section in a couple months, I don’t want to have to request another 60 day FAC eval license after just how long it took the first time).
Thanks for listening!
Leave a comment